[ad_1]
WordPress is a common target for malicious hackers due to the sheer number of people who use it. Some estimates put the total number of WordPress websites on the internet at 455 million. This means that WordPress runs 43.1% of all websites on the internet.

Finding out how many websites get hacked is tricky. There are several reasons for this. Hacking incidents are notoriously underreported. Unless compelled by law to disclose incidents, many administrators and website owners are reluctant to do so. Many are unaware they have been hacked, making it impossible to report.
With these caveats out of the way, IT Governance – a provider of cyber risk and privacy management solutions, reported some 5.1 billion (that’s with a B) breaches in 2021 alone. This figure includes all breaches. Looking at another report, this time by Sophos, 30,000 websites (on average) are hacked daily. This equates to 11 million websites being hacked per year. We know that 43% of all websites run WordPress, which allows us to make an educated guesstimate that 4.7 million WordPress websites are hacked yearly. That’s almost 13,000 WordPress websites hacked every day.
That’s a very large number – which begs the question, why does WordPress get hacked so much? That is exactly what we will look at in this article – based on facts and statistics.
WordPress – how secure is it, really?
WordPress is an open-source project with many people worldwide actively working on it. The WordPress community is very strong and comprises some of the smartest and most committed people you will ever meet. With so many people involved and overlooking the development process, WordPress tends to be very secure.
WordPress’s strength can also be its downfall, as the statistics will show us when we delve deeper into how WordPress websites get hacked.
WordPress’s biggest strengths and weaknesses
No system is perfect, and this also applies to WordPress core. WordPress core represents the core files before any changes (such as plugins, themes, and configurations) are made. In fact, WordPress Core made up 0.58% of all vulnerabilities in 2021 – according to Sucuri’s WordPress hacking statistics report. That is just over half of one percent of all incidents.
Next up are themes and plugins – in that order. In fact, themes make up 6.61% of all vulnerabilities, while plugins make up a whopping 92.81%.
Sucuri further breaks down themes and plugins by whether they are free or premium. While premium themes and plugins make up 8.62% of all 3rd party vulnerabilities, their free counterparts account for 91.38%.
Why good plugins cost money
There are many reasons why this is the case. Plugins and themes come in all shapes and sizes – from reputable developers to shady ones. The truth of the matter is that, when done right, plugin development is not cheap. Full-time professional developers need to be paid while maintaining good infrastructures, and testing facilities also rack up bills.
This is not to say that all free plugins pose a security threat – far from it. Many developers dedicate their free time to producing good quality, free plugins. However, if you want a plugin that is extensively tested and supported, a premium plugin is probably the way to go.
WordPress Vulnerabilities – the numbers
The number of known WordPress vulnerabilities trends upward every year. In fact, WPScan added 1,437 new vulnerabilities to its database and 514 the year before that. In November of 2022 alone, 64 new vulnerabilities were added.
Considering the vulnerability distribution we discussed earlier, these numbers hold up when looking at the number of WordPress plugins available. The WordPress.org repository lists over 60,000 plugins available at the time of writing, with more added daily. Plugins can also be purchased directly from developers or downloaded from unofficial sources.
Due to the ever-changing WordPress vulnerability landscape, targeted attacks are the exception rather than the rule. As old vulnerabilities get patched, and new ones are introduced, hackers can find it difficult to keep up. It also makes targeted attacks very time-consuming, which is why most attacks are automated.
Automated attacks employ the use of a tool to automatically scan many websites, raising alerts whenever a vulnerability is found. Because of this, most attacks are indiscriminate rather than the result of a grudge. But what tools do hackers use for such automated attacks? Let’s find out.
How WordPress websites are hacked
WordPress can be hacked in many different ways – hackers can be very creative in going after targets. This makes it impossible and dangerous to list all the ways a WordPress website can get hacked, as it may provide a false sense of security. However, we can look at one example that illustrates the process a hacker might typically take to hack a WordPress website.
WPScan – A WordPress vulnerability scanner
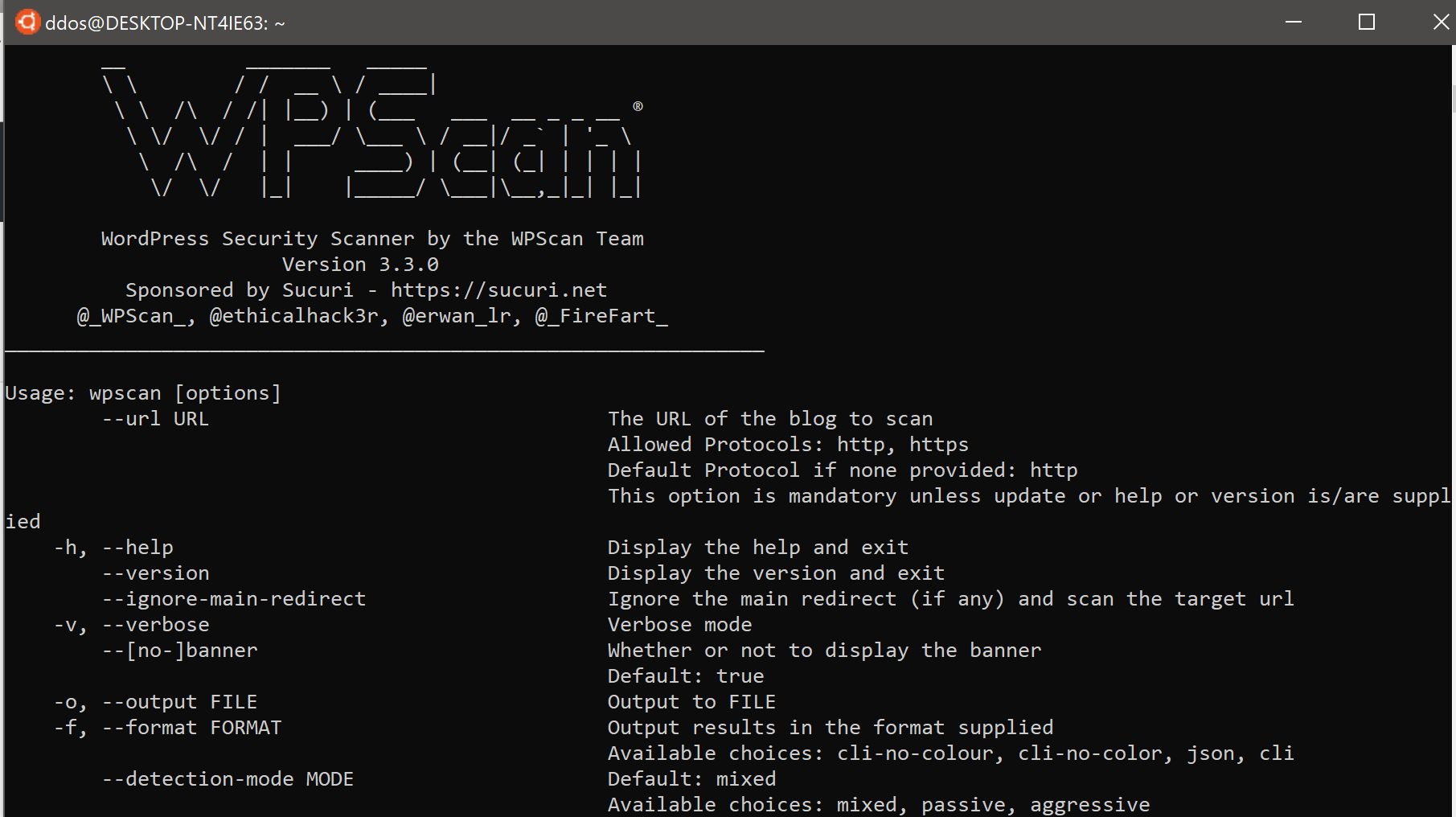
One common tool that is often used by hackers is called WPScan. It is a free tool that is readily available online. It is a vulnerability scanner that scans WordPress websites and identifies known issues and unsecure configurations. When launching a default WordPress security scan with WPScan, you will instantly find out:
- The WordPress version
- Installed plugins, their version, and the path where they are installed
- Installed themes, their version, and the path where they are installed
WPScan includes other functions, such as WordPress user enumeration scans. These scans identify and enumerate all users registered on a WordPress website, giving hackers insight into how your WordPress functions. Armed with this information, the hacker can then launch a secondary attack, such as a WordPress password brute force attack to gain access to your system.
Here, it is important to note why WordPress password security is so crucial to the overall security of your WordPress website. A weak password makes it relatively easy for a brute-force attack to break through. Equally, it is important to ensure all accounts use strong passwords. A compromised contributor account might not be able to inflict much damage, but through privilege escalation on a compromised website, an attacker can gain administrative privileges to wreak havoc.
Why hackers hack
Once a bad actor has managed to gain access to your WordPress website, there are several actions they can take, such as:
- Create a new account with admin privileges
- Reset the password of existing accounts to ensure other users cannot regain access to their WordPress
- Change the role of an existing dormant account
- Change the content to inject it with malicious code
- Tamper with WordPress source code files to add malicious code, such as backdoors
- Add redirects in htaccess files
Protecting your WordPress from attacks
As we have seen, bad actors can take multiple approaches to breach a WordPress website. It stands to reason, then, that securing a WordPress website requires a more holistic approach than simply ensuring users have a password.
- Research – Whether you’re looking for a WordPress hosting provider or a new plugin, be sure to take the time to check them out before. Forums can help you get a quick look at how customers feel about the products or services, while plugins should have frequent updates and great customer support.
- Test – Choosing the best plugin for your WordPress doesn’t have to be a guessing game. Most reputable plugin providers offer a free trial of their premium plugins. This allows you to test them before committing.
Once you have your setup figured out, you’ll need to ensure it is properly configured for maximum security. Configuring a secure WordPress is not a one-time-job but an ongoing process that includes:
- Strong passwords – A strong WordPress password policy can help you ensure brute-force attacks run out of time before they are successful. Use a healthy mix of upper and lower case letters, numbers, and special characters. Also, set a password expiration policy to ensure passwords are changed frequently.
- 2FA – 2FA, short for two-factor authentication, adds an additional authentication layer to your WordPress login. When using 2FA, even if a brute force attack is successful, without access to your smartphone, hackers will not be able to log in.
- Update – Keep WordPress, plugins, and themes up to date at all times. The implementation of WordPress updates can be done in different ways, as this recent survey shows. This can help you balance out administrative and security requirements without breaking a sweat.
- Monitor – Keep a close eye on user and system activity with a security plugin such as WP Activity Log. This will help you identify suspicious behavior early on and shut it down before damage is done.
This is by no means an exhaustive list, but it is a good starting point. WordPress security is an evolving topic, one that requires constant upkeep. Following a WordPress security blog is one way to stay up-to-date and something you can read through as you sip your morning coffee.
Keeping WordPress secure
WordPress security is a cycle rather than a process with a beginning and an end. It requires constant attention and tweaking to respond to evolving threats. While this may sound like it’s too much work, as is often the case, maintenance is better than repair. By dedicating a few hours every month, you can drastically reduce security risks, helping you ensure your website continues to grow.
[ad_2]
Source link